Reading time: 7 minutes
In this edition of the Building Perspectives series, Dr. Andreas Kaup explains why a high-performance and secure IT infrastructure is the essential prerequisite for future-ready smart buildings—particularly when digitizing existing properties. As a Senior Consultant at ComConsult and a recognized expert in IT infrastructures, network technologies, and data center planning, he provides practical insight into how integrated network and security concepts establish the foundation for scalable, efficient, and interoperable building operations.
Smart buildings are properties featuring modern digital infrastructure, highly available connectivity, up-to-date IT, a foundation for the Internet of Things (IoT), and intelligent building automation. All information and functionalities are consolidated within a management platform. To realise such a holistic approach, network and IT infrastructure must be considered from the outset during planning, as they form the building’s nervous system. This enables various cross-trade functionalities and a digital user experience. At the same time, data availability can significantly improve the energy efficiency of the building.
Additionally, future building operations require an operator data model that brings together the needs of technical and commercial building management—a connection between facility and real estate management without any breaks in information or data1. One potential solution is the consolidation of all relevant information for building operations in a central digital administration shell. Regardless of the approach, the objective is to enable consistently digitalised, interoperable, secure, and efficient building operations.
For scalable solutions regarding efficient building operation, it is essential to focus on existing properties. It is an easily grasped fact that existing buildings make up a significantly larger proportion than newly developed smart buildings. Numerous studies examine what percentage of the buildings used in 2050 already exist today, and none available to me at this time name less than two-thirds.
If resource-efficient smart buildings are needed for the future, but the majority of buildings already exist, many will need to be transitioned into a new lifecycle and made ‘smart’. This article focuses on non-residential buildings, particularly commercial and industrial properties. In recent years, awareness of the importance of IT security has generally increased. However, IT/OT security within building technology still plays a very minor role. Buildings developed as modern in the 1990s and 2000s now need to be transitioned into a new lifecycle, due to the nature of things and exponential technological development. Even in what were once the most advanced buildings, it was not possible to develop (network) infrastructure that meets today’s requirements—simply because those requirements did not exist at the time.
When originally self-contained systems, never intended for cross-trade communication or connection to cloud and remote access, are to be integrated into holistic building operation concepts, IT/OT security measures must be implemented.
IT/OT Security: Status Quo
When conducting IT/OT check-ups of existing properties, it is standard to encounter several of the problems listed below. These risks are a selection from many genuine, self-determined project results.
- Dedicated and unsecured remote maintenance access: Some systems in buildings use more or less secure VPN tunnel connections for remote maintenance. However, this does not have a significant impact on the security of the entire network if other systems in the same network use unsecured access. In an era of cross-trade concepts, it is no longer sufficient to look only at one’s own security.
In almost every large existing property, there will be at least one router used for remote maintenance purposes, which no one knows the origin of and/or on which old standard passwords are used.
- Switch cascades: In a matured structure, it is not unusual for a sort of unmanaged switch daisy-chaining to be quickly implemented for the uncomplicated modernisation of a sub-system or floor. The automation focal points and field devices behind the unmanaged switch are not easily found again.
- Missing or insufficient documentation: This concerns both network topologies that are not up to date and frequently completely missing asset inventories. You can only protect what you know.
- Single-point-of-knowledge: There is a significant risk that many individuals who have been operating a building since it was commissioned will retire soon, and much knowledge about the developed structures will disappear into well-earned retirement if it has not been secured long-term through processes.
- Old (server) operating systems and end-of-service components: For many systems and components, update and patch management has not been applied or needed for years, as these were self-contained systems.
- Unencrypted communication: Encrypted communication for IP-based communication protocols is still new territory in building technology, and thus even less common in existing properties.
- Unsecured wireless interface: Many devices operated with standard passwords broadcast an SSID without the operator being aware that these devices support wireless technologies at all. These might be the room automation station, the lighting gateway, or the microwave. Sometimes the wireless interface is a simpler way in than the front door.
This list does not claim to be exhaustive and could easily be expanded. It is important to note that this enumeration is explicitly not a criticism of existing buildings. After all, it is the natural result of structures that have grown during operation. As is so often the case in life, it is now crucial not to repeat the same mistakes and to bring existing buildings into the future—not piece by piece or trade by trade. Therefore, a modernised building needs not only holistic operation, but also a thoughtfully designed network concept.
BSI IT Baseline Protection
The majority of the weaknesses listed above can be addressed by following the basic and standard requirements, as well as the associated implementation guidelines from the German Federal Office for Information Security (BSI), the BSI IT Baseline Protection modules INF.13 Technical Building Management and INF.14 Building Automation2. Although these are categorised under building automation and are guidelines made for Germany, the requirements can nonetheless be applied to all building technology. In Table 1 , each of the security risks mentioned above is matched with corresponding BSI requirements (A) and implementation guidelines (M) from their module INF.14. Such a mapping could also be carried out analogously to the fundamental requirements of IEC 62443-3-32.
| Risk | Requirement / Implementation Measure | Excerpt |
|---|---|---|
| Dedicated and unsecured remote maintenance access | INF.14.M1 Planning of building automation INF.14.A14 Use of access protection suitable for building automation Defined in module OPS.1.2.5 Remote Maintenance |
INF.14.M1: “In the detailed planning of building automation networks, at least the following points should be appropriately considered: (…)”
|
| Switch cascades | INF.14.M11 Securing freely accessible ports and access points in building automation Defined in modules NET.1.1 Network Architecture and Design, NET 1.2 Network Management. |
INF.14.M11: “When cascading multiple switches, it may happen that the higher-level switch used for authentication does not notice when a building automation-relevant component is switched off or unplugged.” |
| Missing or insufficient documentation | INF.14.M5 Documentation of building automation | “All building automation [and building technology] must be sustainably documented. The documentation produced must be regularly reviewed and updated to ensure that it always reflects the current status (…).” |
| Old (server) operating systems and end-of-service components | INF.13.A11 Appropriate hardening of systems in Technical Building Management Defined in module OPS1.1.3 Patch and Change Management |
INF.13.A11: “For all systems (…), it SHOULD be ensured during procurement that they can be appropriately hardened and, in particular, that security-relevant updates are provided for the planned period of use.” |
| Unencrypted communication | INF.14.A12 Use of secure transmission protocols for building automation | “Outside trusted network segments, communication via Ethernet and IP between building automation systems SHOULD be encrypted.” |
| Unsecured wireless interface: | INF.14.A16 Securing wireless communication in building automation networks | “In particular, appropriate authentication and encryption SHOULD be implemented on the wireless interface.” |
Smart Building Topology
Whether for new builds or existing properties, a smart building topology is a useful tool for visualising all use cases, trades, interfaces, functions, and communication protocols in a single diagram—see Figure 1.
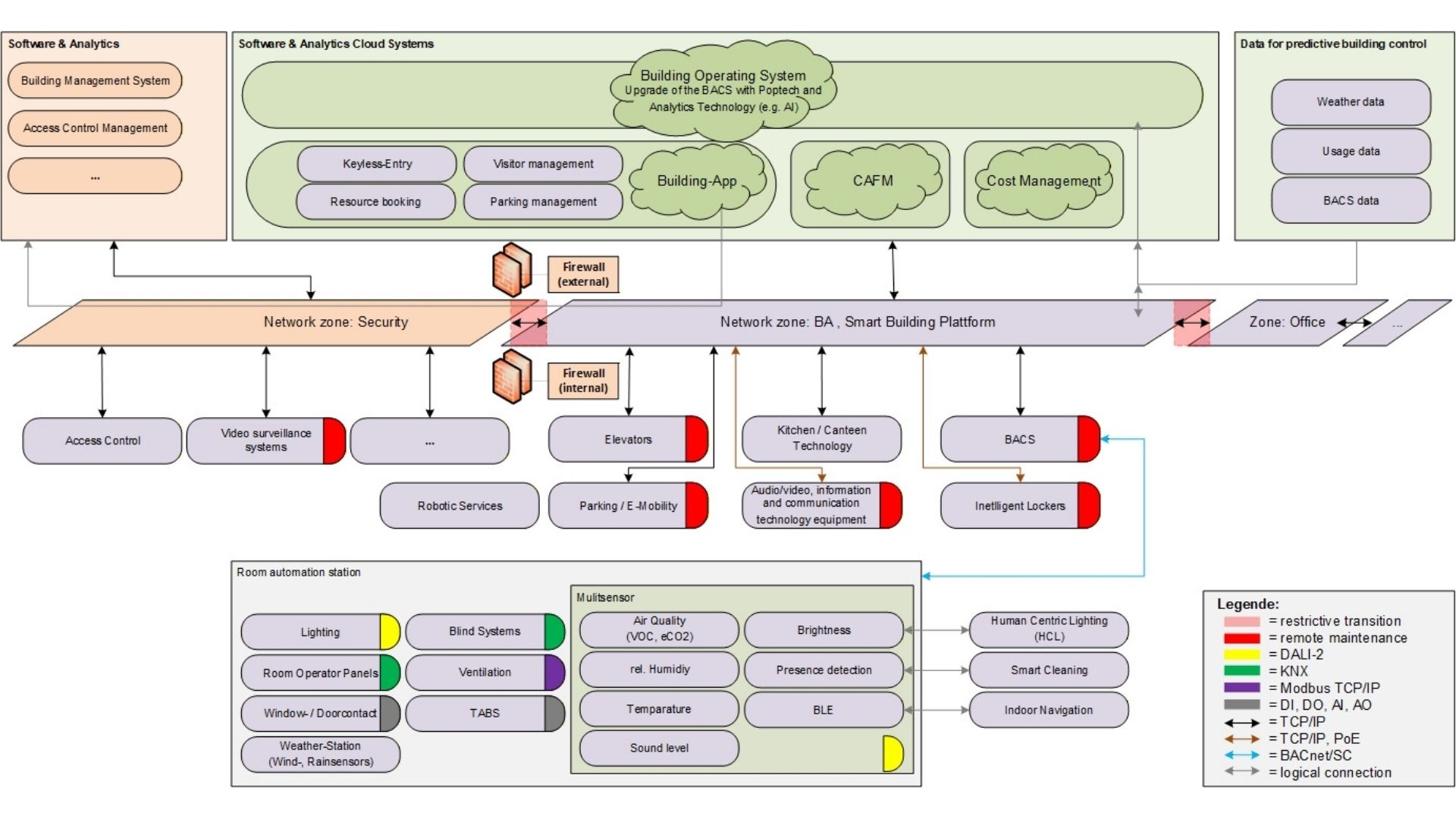
Figure 1: Example of a simplified smart building topology, adapted from1. The topology visualises IP-based communication paths for various building trades. Network zones and network transitions are shown, as well as cloud systems and connection to the Internet. Of particular relevance are also the remote maintenance accesses and, not least, the listing of all software systems present in the overall context.
Such a topology provides significant added value for planning network and IT security. Fundamentally, the topology gives an overview of which trades need to be considered in a network concept and to which zone they are assigned. Another important piece of information is the need for remote maintenance. Where possible, a centralised remote maintenance access can be provided, through which all remote accesses are enabled. This helps to avoid the initial status quo seen in existing buildings, where there are countless separate, mostly unsecured remote maintenance solutions within the property.
Some IT security features are already directly documented within the topology:
- a two-stage firewall concept with demilitarised zone (DMZ),
- restrictive network transitions,
- secure communication protocols in building automation (BACnet Secure Connect, KNX IP Secure),
- redundant internet connection.
Furthermore, the topology allows identification of IT security requirements that should be addressed in an IT security policy and concept, both in terms of requirements and implementation:
- cloud security
- application and API security
- data protection
- cryptography
- wireless communication (WLAN, BLE)
Beyond this, further procedural added value can be derived, as many interfaces and data uses that make operations more efficient must first be clearly defined and approved. Corresponding approval processes with staff councils, data protection officers, and IT governance can only be initiated in good time if these are known and comprehensible at an early stage.
The IT/OT security of existing buildings is an important and underestimated risk. In many buildings, individual measures have already created unknown IT security vulnerabilities. In the remaining buildings, upcoming modernisation projects at least carry the risk of generating new IT security gaps. Solutions for avoiding the IT/OT security gaps discussed here already exist. The first task, however, is not yet to close the security gaps, but to create awareness that they exist. After all, you can only protect what you know.
Bibliography
1 D. A. Kaup, „Smart Building und IT-Sicherheit: Alles ist verbunden,“ Februar 2026.
2 BSI, IT-Grundschutz-Kompendium, BONN: Reguvis Fachmedien GmbH, 2023.
3 IEC, IEC 62443-3-3:2013 Industrial communication networks – Network and system security – Part 3-3: System security requirements and security levels, 2013.